Comodo Cyber Solutions
IT’S NO SECRET THAT ENDPOINT PROTECTION IS THE MOST CRITICAL COMPONENT IN YOUR IT SECURITY TECHNOLOGY STACK.
FOR TRULY COMPREHENSIVE AND ROBUST DEFENSE IN THE CURRENT THREAT LANDSCAPE

In a world where preventing all cyberattacks is impossible, Comodo Cybersecurity provides Active Breach Protection with its cloud-delivered cybersecurity platform. The Comodo Cybersecurity Platform provides a zero trust security environment that verdicts 100% of unknown files. The platform renders an almost immediate verdict on the status of any unknown file, so it can be handled accordingly by either software or human analysts. This shift from reactive to proactive is what makes Comodo Cybersecurity unique and gives us the capacity to protect your business – from network to web to cloud – with confidence and efficacy.
Comodo has experts and analysts in 185 countries, protecting 100 million endpoints and serving 200,000 customers globally. Based in Clifton, New Jersey, Comodo Cybersecurity has a 20-year history of protecting the most sensitive data for both businesses and consumers worldwide.
- Comodo AEP
- Comodo Dome
- Secure Web Gateway
- Secure DNS
ENDPOINT PROTECTION WITHOUT COMPROMISE
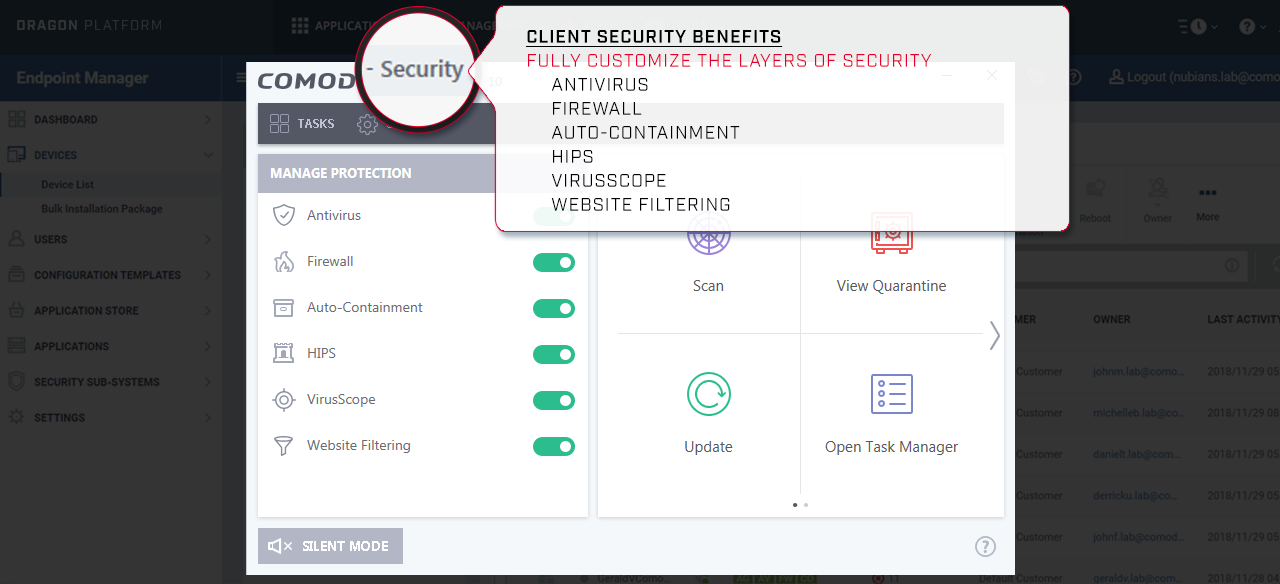
The cyber-threat landscape has evolved and so has endpoint protection.
Different solutions use different approaches and before you make a decision for your organization,
you need to understand the options—and the tradeoffs.
“Signature- and behavior-based detection tools use a “default allow” approach to endpoint security. They let everything in and then determine if there is any malicious code being run. In contrast, sandboxing and containment take a “default deny” stance, preventing anything from running until it’s deemed safe.
While this offers much tighter security, what happens between the time the file enters the system and when a safe file is cleared and passed back to the end user? Security is critical, but it can’t come at the expense of business productivity. Comodo Advanced Endpoint Protection (AEP) solves this problem.”
Key Features
Comodo
Antivirus
Auto
Containment
Cloud-based
Online Platform
24x7
Human Analysis
VirusScope
Behavioral Analysis
Scans endpoints against a massive list of known good and bad files compiled from years as the world’s largest certificate authority and from the 85 million endpoints deployed worldwide.
Unknown executables and other files that request runtime privileges are automatically run in Comodo’s patented virtual container that does not have access to the host system’s resources or user data.
Automatic signature updates that simplifies deployment across your entire environment to lower operational costs delivering reliable, centralized and fully scalable security solutions for today’s business
In the 5% of cases where VirusScope and Valkyrie are unable to return a verdict, the file can be sent to researchers for human analysis who make a determination within SLA timelines.
Uses techniques such as API hooking, DLL injection prevention, and more to identify indicators of compromise while keeping the endpoint safe and without affecting usability.
Valkyrie Verdict
Decision Engine
Fileless
Malware Protection
Host Intrusion
Prevention
Personal packet
filtering firewall
Interoperability
While running in auto-containment, unknown files are uploaded to a global threat cloud for real-time analysis, returning a verdict within 45 seconds for
95% of the files submitted.
Not all malware is made equal. Some malware do not need you to execute a file, it built-in the endpoint’s memory-based artifact such as RAM. Comodo AEP completely stops write access against this threat
Rules-based HIPS that monitors application activities and system processes, blocking those that are malicious by halting actions that could damage critical system components.
Provides granular management of inbound and outbound network activities, hides system ports from scans, and provides warnings when suspicious activities are detected.
A solid defense-in-depth security strategy requires enterprises to deploy a diverse security toolkit using technologies from a range of vendors. In a heterogeneous-bydesign environment, interoperability is crucial.
Cloud Delivered Secure Web Platform
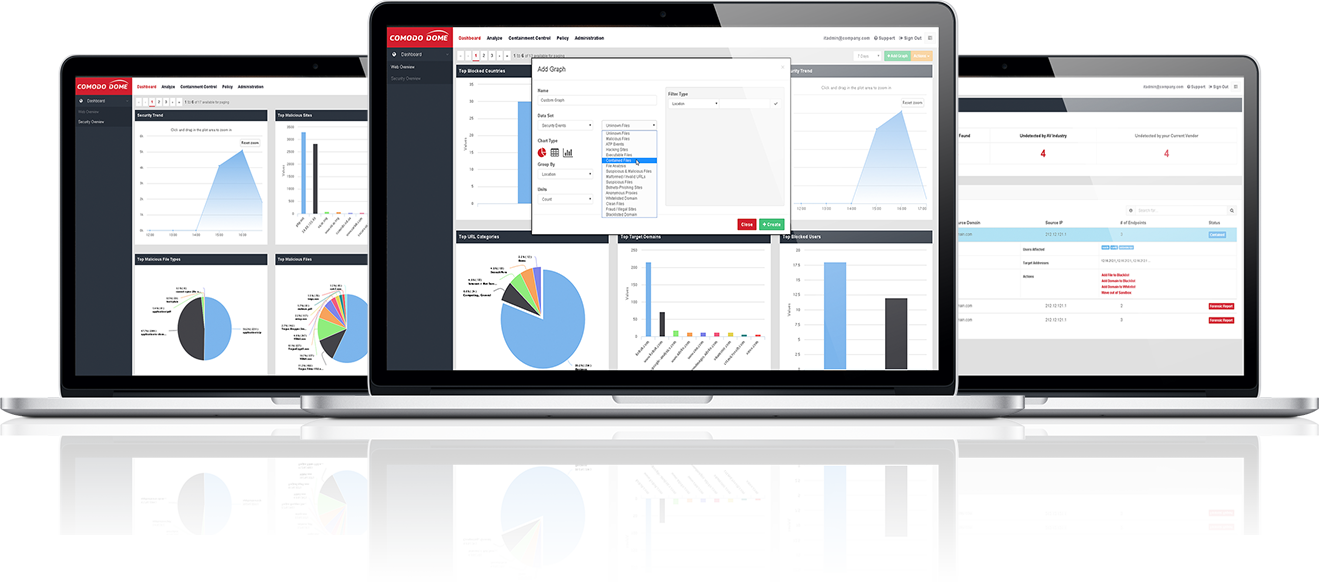
Traditional web content security has almost always been built on a default allow architecture combined with black listed files and signature-based detection, but with new malware variants being created at over a half million a day, this approach has quickly become untenable and alarmingly ineffective. Any solution that relies on “patient-zero” infections to subsequently generate and eventually distribute signatures, all but guarantees that new unknown files will lead to new infections. This is the fundamental flaw in today’s web security landscape.
Comodo Dome radically shifts protection from the standard default-allow to our unique Default Deny Platform still allowing uninterrupted business productivity while protecting your users from advanced targeted attacks. Comodo’s patent-pending containment combined with Valkyrie, our cloud-based platform, renders verdicts within 30 seconds, affording Comodo Dome customers automatic protection from any and all new and unknown payloads without the need to rely on signatures or outdated file-type blocking.
“Comodo Dome, with revolutionary portable containment technology, ensures 100% protection from even unrecognized emerging threats.”
– Zach Forsyth –
– Product Line Manager, Comodo –
Complete Your Security Layers
Sophisticated and highly customized attacks are becoming the norm, not the exception and are being aimed directly at inadequately protected end points inside – and more importantly – outside the corporate network where protection levels are almost uniformly lower.
Adding Comodo Dome between your existing infrastructure and the internet couldn’t be easier - simply make Dome your next hop to the Internet. As a cloud-based solution, there’s no hardware appliances or headaches, and in minutes you’ll have added the bulletproof layer of security and compliance that you’ve been missing.
The Solution
Comodo Dome is a revolutionary Cloud Delivered Secure Web Platform that is delivered as a Security as a-Service (SaaS) solution that provides fully comprehensive web content security and control, regardless of user, device or location, and scans all inbound and outbound traffic in real time to ensure protection from the latest threats as well as strict compliance with corporate policies.
Rethink Your Security and Network Architecture
The Comodo Dome Cloud Security Platform is totally modular and acts as a highly advanced series of security check posts encompassing Advanced Threat Protection, Web Security, portable containment, Sandboxing, Antispam, DLP, Next Generation Firewall, and Bandwidth management. Simply choose the modules you require today, and seamlessly add new ones in the future.
Comodo Dome protection nodes are available in more than 140 countries around the world – so that you can effortlessly secure all of your users, offices, stores, and even the smallest remote locations, all without the overhead of physical appliances. At the same time, you can also massively reduce or even totally eliminate MPLS and private network costs while slashing your hardware footprint.
Advanced Protection in The Cloud Era
There is an enormous migration underway. With storage, business applications and services all moving to the cloud, the traditional approach of installing a large centralized web security gateway device and then backhauling all of your traffic from remote offices, devices and users has quickly become exceptionally cumbersome if not obsolete. It makes far more sense to forward traffic to a centralized cloud platform that can provide protection regardless of network origin and destination.
Comodo Advanced Containment
Sandboxing is becoming a commonplace security strategy, but it typically hinders business productivity by isolating unknown and suspect files in a state where they cannot be used until after a thorough analysis is complete. Comodo’s unique containment technology is radically different. While Valkyrie analyzes unknown files, users are free to open, execute and use the files with ZERO risk of infection. Comodo’s containment technology is agentless, extremely lightweight, has no CPU dependencies and is application-agnostic.
Valkyrie Cloud-Based File Verdict Platform
Valkyrie has the fastest file verdict capabilities in the industry and utilizes a combination of static, dynamic and advanced behavioral analysis to inspect files as they’re being downloaded. It quickly renders risk verdicts for any file – normally within 40 seconds – five times faster than our closest competitor. The most dangerous files are classed as unknown and are immediately placed into a contained state before being delivered to the end user. At the same time, the file is undergoing an even more extensive analysis, including examination by human experts at Comodo’s Advanced Threat Research Labs. When a final verdict arrives, the file is either released from containment or deleted and blocked (blacklisted).
Comodo’s Default Deny Platform is one of the essential keys to effective web security as it allows known-good applications, while denying known-bad and containing any unknown files until a verdict is reached. In the meantime, users can remain productive by running unknown files safely and securely within a portable container that doesn’t require any new infrastructure, software or agent installations.
As the #1 certificate authority brand in the world, Comodo is uniquely positioned to identify known-good software publishers and applications for auto-whitelisting; while our installed base of over 85 million users provides the Comodo Threat Research Labs (CTRL) with one of the largest caches of known-bad files (blacklists) anywhere in the world.
Secure Web Gateway
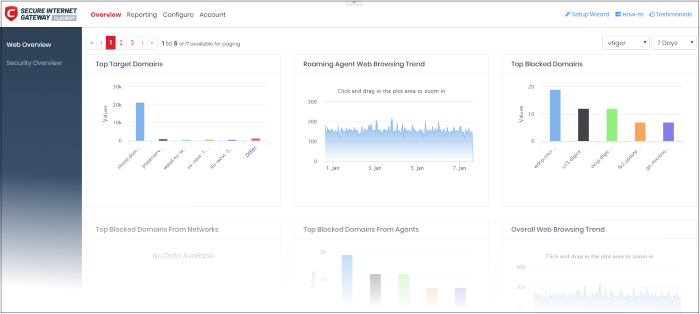
Securing access to the web — from anywhere As small and mid-sized businesses embrace the opportunities of the cloud and Internet they must also address the cybersecurity risks inherent in digital transformation. Cloud-based applications and other Internet-based services open up channels of communication to and from the corporate network that make businesses vulnerable to cyberthreats and the loss of critical data.
For small and mid-sized businesses without the dedicated IT and security resources of larger enterprises, Comodo Cybersecurity offers Comodo Secure Web Gateway. A 100% cloud-delivered service, Comodo Secure Web Gateway protects businesses from the full range of web-borne cyberthreats—known and unknown—without any IT footprint or security staff.
At-a-glance
- Secure web access for small and mid-sized businesses – from anywhere
- Enterprise-class security with zero IT footprint or security staff
- The perfect balance of security and usability through patent-pending threat containment and analysis
- Unmatched visibility into threat activity worldwide via intelligence gathered from 85 million endpoints under Comodo’s management
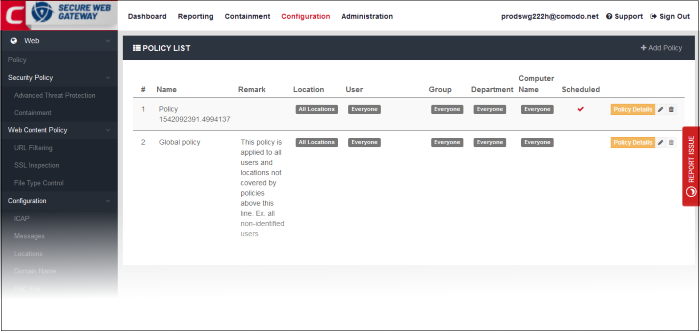
Comodo’s Secure Web Gateway provides enterprise-class security to small and mid-sized businesses through a unique set of features
Policy enforcement and visibility
URL and content filtering
Advanced threat protection
Containment and analysis of unknown applications
Define groups by user, department, location and mobility for granular policy management and visibility; easy integration with Active Directory.
Filter content based on 60+ categories, create custom blacklists and whitelists, enforce safe search, enable country-based blocking and hash-based blocking.
Protect your business from all web-borne threats including phishing attacks, malware, botnets, C&C callbacks, spyware, drive-by downloads, XSS-injection, cookie stealing, anonymizers and encrypted files.
Contain and analyze all unknown executables to eliminate attacks without slowing down your business.
File-type control
SSL inspection
Real-time, fully customizable reporting
Traffic forwarding
Multi-office, multi-location and mobile user protection
Block content by true file-type, hash, source and category.
Fully inspect encrypted web traffic.
Gain visibility into Internet activity by user, group, device and location through easy-to-build custom reports.
Forward traffic using a simple agent, proxy chaining, ICAP or direct proxy/PAC.
Protect all of your users and offices regardless of location.
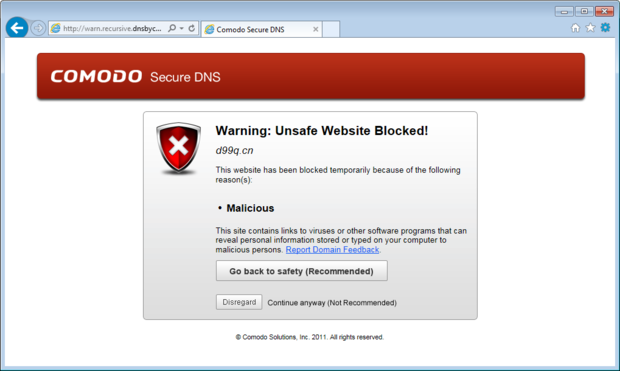
Secure DNS Filtering
SOLUTION OVERVIEW
Cloud-based solution that blocks malicious websites
Secure DNS Filtering is a cloud-based solution that blocks websites by 83 categories and blocks advanced threats like phishing, malicious domains and endpoints communicating with command and control servers. Secure DNS Filtering can be used for controlling, monitoring and securing the web access of your users by their locations, internal IP addresses, networks, any type of mobile devices, and devices both on and off the network.
Paired with the largest threat intelligence lab in the market
Our Threat Intelligence Labs monitors, filters and contains, and analyzes malware, ransomware, viruses and other “unknown” potentially dangerous files 24x7x365 in over 190 countries around the world. With 5 offices spread across the Americas, Asia, and Europe (and staff covering over 190 countries), the Lab is made up of more than 120 IT security professionals, ethical hackers, computer scientists and engineers (all full-time Comodo Lab employees) analyzing millions of potential pieces of malware, phishing, spam or other malicious/unwanted files and emails every day. The Lab also works with trusted partners in academia, government and industry to gain additional insights into known and potential threats.
Advantages to implementing DNS Filtering
- Visibility and Protection for all Internet Connected Devices, Anywhere
- Ubiquitous Web Access
- Policy Enforcement
- Faster browsing
- Reduced Costs for Cloud Security
- Deployment in minutes
- Compliance: CIPA
Comodo’s Secure Web Gateway provides enterprise-class security to small and mid-sized businesses through a unique set of features
Policy enforcement and visibility
URL and content filtering
Advanced threat protection
Containment and analysis of unknown applications
Define groups by user, department, location and mobility for granular policy management and visibility; easy integration with Active Directory.
Filter content based on 60+ categories, create custom blacklists and whitelists, enforce safe search, enable country-based blocking and hash-based blocking.
Protect your business from all web-borne threats including phishing attacks, malware, botnets, C&C callbacks, spyware, drive-by downloads, XSS-injection, cookie stealing, anonymizers and encrypted files.
Contain and analyze all unknown executables to eliminate attacks without slowing down your business.
File-type control
SSL inspection
Real-time, fully customizable reporting
Traffic forwarding
Multi-office, multi-location and mobile user protection
Block content by true file-type, hash, source and category.
Fully inspect encrypted web traffic.
Gain visibility into Internet activity by user, group, device and location through easy-to-build custom reports.
Forward traffic using a simple agent, proxy chaining, ICAP or direct proxy/PAC.
Protect all of your users and offices regardless of location.
